1 Million Leaked Credit Cards on Dark Web – 2021
In early August 2021, a threat actor known as AW_cards published a data leak containing details of approximately one million stolen credit cards on several Dark Web hacking forums. The leak was shared free of charge as a promotion to the threat actor’s new carding marketplace, named AllWorld Cards.
The stolen credit card records include credit card and owner details, including credit card number, expiration date, CVV number, holder’s name, country, state, city, address, zip code and email address or phone number. In our research of the data of 1M leaked credit cards on the Dark Web, we analyzed the leaked email addresses to gain a better understanding of the risk.
Analysis of the leaked credit cards and email addresses
We analyzed all the email addresses that appeared in the leak and found approximately 600,000 email addresses were exposed. The most common email domains that appeared include:
- Gmail.com – 419,000 email addresses
- Hotmail.com – 65,540 email addresses
- Yahoo.com – 20,570 email addresses
- Outlook.com – 10,150 email addresses
- Icloud.com – 6,920 email addresses
- Ezrecharge.in – 5,530 email addresses
- Payu.com – 4,580 email addresses
- Hotmail.co.uk – 3,680 email addresses
- Libero.it – 3,570 email addresses
- Ezsms.in – 2,730 email addresses
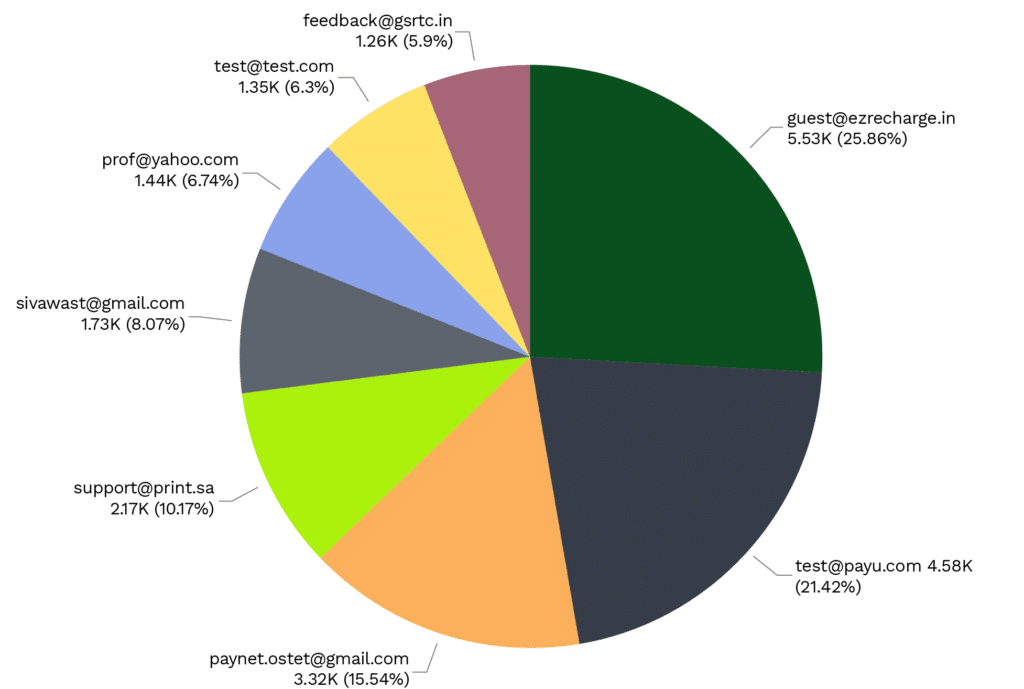
Following are the top email addresses that appeared in the leak:
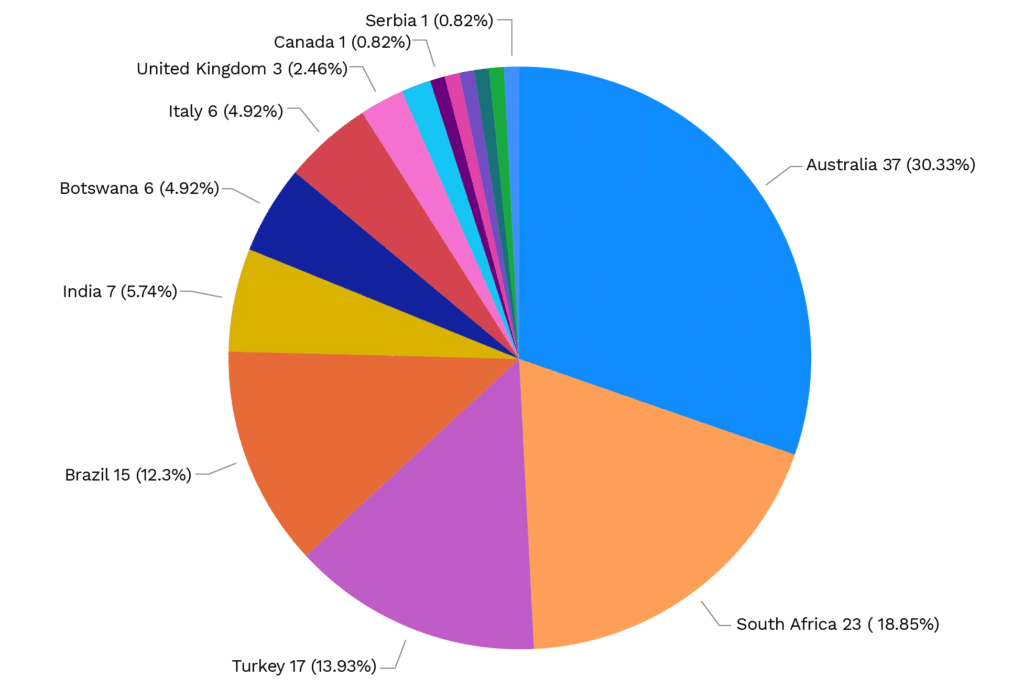
In addition, we identified 122 government-related email addresses, i.e. email addresses that end with a .gov TLD. These 122 records are associated with a total of 15 countries.
The distribution of governmental addresses per country is as follows:
About the threat actor’s goal
AllWorld Cards is a new card marketplace, active since May 2021. At the time of this publication, the marketplace holds an inventory of over 2,749,336 credit cards, with an average price per card of $US 6. Since late May 2021, the threat actor has been actively advertising and promoting the new platform on different Dark Web hacking-related platforms. The current leak of one million credit cards by the threat actor appears to be another marketing move to attract potential clients from hacking and cybercrime forums and increase the platform’s popularity.