How to Avoid 2020 Online Shopping Threats
The shopping season is upon us and as in previous years, cybercriminals are preparing multiple ways to target the online shopping community, including phishing attempts to steal financial details, malspam campaigns distributing malware and more. In fact, while examining the credit card trade in the Dark Web during 2019, we discovered that the highest number of stolen cards offered for sale on dedicated marketplaces was in November 2019 with over 32M cards, although we should take in consideration that there are duplications of data, since it is likely that cybercriminals will try to sell the stolen data in multiple marketplaces.
In this post we will provide you with some tips for ensuring a secure shopping spree and we will also take a look at recent attacks and how attack groups operate to target online shoppers and vendors.
Are you shopping online this season? Here are essential Do’s and Don’ts for you:
- Be extra aware of phishing attacks, especially with emails requesting you to verify or update your account details, register to get a free item or a coupon, etc.
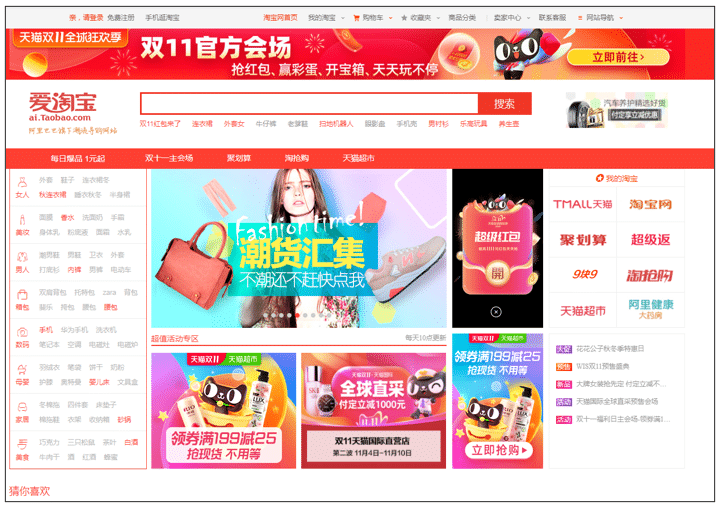
- Verify the URL address of the platform you are about to buy from – make sure the URL address of the official website of the desired brand.
- Check that the platform you are shopping on to purchase goods is secured – look for an HTTPS URL, a trusted certificate, etc.
- Do not open attachments sent from unknown sources, especially ones requesting to enable macro or editing permissions in order to open them.
- Avoid clicking on ads of any kind, especially during the shopping season.
- Do not download apps from unofficial App stores, especially shopping-themed apps.
- Check apps permissions and update your mobile operating system on a regular basis.
- Use 2FA or OTP protocols if provided by the service vendor.
What you see isn’t always what you get: Scam Websites and Fake Domains
Fake domains of popular brands can be used in. spam or phishing campaigns that are carried out via mail, SMS, social media platforms and more. In last year’s shopping season, 124,000 suspicious domains were detected, abusing names of 26 brands. The most targeted brands were Apple, Amazon and Target.
This year, we researched how many domains with the word “Amazon” were registered during the first week of November 2020. We detected over 600 of recently registered domains with no official connection to Amazon in their registration details. Although it seems that many of them are not yet “operational”, as they do not lead to an active website, some of them sure look suspicious, for example: verification-amazonservices.com (detected as a phishing website via several AVs), account-verificationamazon.com, amazon-login-verify.com (detected as suspicious by one AV) and even amazon-black-friday.com (first created in 2010 and is being re-registered each year since then.
Scam websites usually use a similar web design and interface to the legitimate online shopping platforms, and therefore it is recommended to check the website’s domain or URL address before purchasing goods using your credit card.

Keep your systems updated to avoid E-skimming attacks (AKA: Magecart attacks)
E-skimming is one of the most popular ways these days to carry out credit card fraud. Cybercriminals usually exploit a vulnerability in the e-commerce or online payment platform (usually in third parties’ components), in order to inject a malicious code that will capture the user’s credit card data and send it the its operators. Once they hold the data, cybercriminals will probably sell it in the Dark Web or use it to make additional purchases.
Magecart is the name given for this type of attack and to cybercriminals that usually target platforms running outdated versions of Magento (while exploiting flaws, such as CVE-2017-7391 and CVE-2016-4010 in Magento) and use a malicious JavaScript code embedded into the compromised platform (sources: www.darkreading.com & www.trustwave.com). In fact, Magecart attacks are so common that in September 2020, it was reported that approximately 2,000 e-commerce platforms were targeted in one weekend.
Additional ways to carry out e-skimming attacks are by accessing the e-commerce network, using administrative credentials. These can be obtained via phishing, brute-force attacks, or a cross-site scripting attack that redirects users to a malicious website with a JavaScript code. Access to networks of online shopping platforms are also traded on Dark Web forums, allowing threat actors to gain access to databases containing users’ details.
Of note, nation-state groups were also spotted using this attack vector in the wild. In July 2020, researchers found that the North Korean group Lazarus was behind a serial of Magecart-style attacks against multiple e-commerce stores around the world.
Therefore, it is vital for organizations that operate online payment platforms to keep them updated and secured. We really can’t stress this enough. It is also recommended to use tools that will help detect such malicious injections and monitor suspicious activities in order to block them on time.
The spamming season: Spam campaigns are used for malware distribution
In the shopping season of 2018, a massive spam campaign distributing Emotet, targeted online shoppers worldwide, especially in North and Latin America and the UK. Emotet is an infamous malware, active since 2014, that was first detected as a banking Trojan, but these days it is often used as a downloader or a dropper for additional Trojans or even ransomware. It is usually distributed via worldwide spam campaigns and malicious attachments that request users to unable Macros. During last year’s shopping season, approximately 130 million malware attacks and ~640,000 ransomware attacks were detected in the US. Based on what we’ve seen in the past few years, it is expected that malware operators will try to lure victims via shopping-themed emails and malicious attachments.
The world goes mobile: The rise in malicious mobile apps
Each year, malicious shopping-themed apps target unaware users during the shopping season, which is why it is recommended to download mobile apps from official platforms and to check the reviews. However, in January 2020, a new Trojan dubbed “Shopper” was spotted leaving fake applications reviews on Google Play, on behalf of the infected device’s owner, leaving users with no trust in apps rating. The Trojan was also detected turning off the Google Play Protect feature, in order to download additional apps without safety checks, using the victim’s Google or Facebook account to register to popular shopping and entertainment apps, spreading advertisements, etc. Infections were spotted worldwide, including in Russia, Brazil and India.
Additional malicious shopping season-themed Android apps were spotted in 2019 luring users with coupons, discounts and other shopping hacks. Some of them were detected sending sensitive information from the infected devices to their operators or containing adware used to spread malicious advertisements (sources: securitynews.sonicwall.co & www.trendmicro.com).
To Conclude, Be Aware
The shopping season is open for all, including cybercriminals who are trying to maximize their gain. Awareness is the key when it comes to what shoppers can do to keep safe, whereas vendors need to take additional measures during these times to avoid financial loss, reputational damage and customer abandonment.