5 Reasons Why Criminals & Terrorists Turn to Cryptocurrencies
The frenzy surrounding cryptocurrency is nearing epic proportions, as cryptocurrency usage surges and Bitcoin valuations hit record highs. But not all aspects of this phenomenon are a blessing. Just as cryptocurrencies are gaining traction with consumers as legitimate transactions, they are also increasingly used by criminal actors, with a global total of $10 billion in illicit activities in 2020. The rise of cryptocurrency crime is a major issue facing law enforcement agencies as the blockchain changes the nature of financial investigations. Cryptocurrency financial investigations have become a new standard, making it vital to understand the motives behind crypto criminals.
The dubious and illegal side of cryptocurrencies
Cryptocurrencies serve as a financial enabler to a multitude of illegal and disreputable purposes such as:
- Money laundering
- Fraud
- Drug trafficking
- Human trafficking
- Child exploitation
- Dark marketplace trading
- Cybercrime
- Terror funding
Consequently, government security organizations are directing their resources to crypto criminal investigations, with the aim of tracking illicit transactions and identifying the parties involved. But this is a very difficult and complex task – and this is exactly why criminals and terrorists opt to use cryptocurrencies.
Under the mattress: hiding criminal cryptocurrency
There’s no need to explain why criminals and terrorists prefer not to open bank accounts to store their ill-gotten gains. Banks are highly regulated institutions and are subject to specific requirements, restrictions, and guidelines. Banks require identification documents, as they are bound by KYC (Know Your Customer) regulations, legal statements to approve large transactions to comply with anti-money laundering regulations, and governmental sanctions may be applied at any time in the form of accounts frozen or seized.
In the movies, criminals and terrorists move money around in suitcases or duffle bags and store it under the mattress or in the floorboards. In reality, large amounts of money are difficult and risky to move around in this way, specifically when it comes to international transfers.
So, the storage of choice for criminals and terrorists is cryptocurrency. But why is it so attractive?
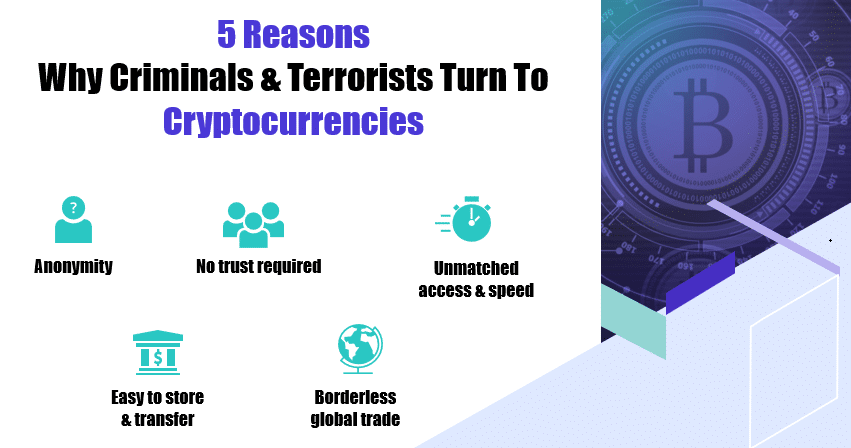
Why criminals use cryptocurrency
#1: The promise of anonymity
While all transactions that occur on the blockchain are kept on the public record and are accessible to anyone for review, the identities of transaction makers remain unknown.
Transactions are made from one or more crypto addresses to one or more destination addresses. A crypto address is a random set of characters, which is roughly the crypto equivalent of a bank account number.
Anticipating payment of funds? You send your address to the delivering party, who uses this address to deliver the funds. But there is no link between the address – a random set of characters – and its owner. So, while the transaction data is public, the transaction maker remains anonymous.
This way, criminals can, seemingly anonymously, trade drugs, weapons, explosives, child pornography, and more. Similarly, terrorists can ask for funding and donations for extremist organizations, without revealing their identity.
#2: No strings attached
Cryptocurrencies are transferred between peers, with no former acquaintance between the parties required. No third party is involved or needed as a mediator.
This is largely exploited by criminals for one-off sales of drugs or digital data (e.g. child pornography) as well as for terror funding across borders.
#3: Unmatched access and speed
Trading with crypto is so easy. It requires just an internet connection, a wallet application that is quickly and easily downloaded to your device, or just using a cloud service, and…that’s it. In a few clicks you can transfer money, or a monetary equivalent, anywhere in the world.
Cryptocurrencies are digital assets, controlled by no central authority, hence they are always available, and there is no need to validate the transaction with a central body or third party. In addition, there are usually no delays, as we experience, for example, when transferring money internationally between bank accounts.
Cryptocurrencies are transferred within minutes and there’s no way to reverse the transactions once they are confirmed by the miners.
Take the example of the Twitter hack, an attack in which Twitter accounts are compromised to post fake tweets that appear to promote a cryptocurrency scam. In a notable case of Twitter hack in 2020, accounts belonging to Joe Biden, Barack Obama, Bill Gates, Kim Kardashian and several other high profile individuals were hacked, while a Bitcoin wallet which appeared in some of the tweets received more than $100,000 worth of Bitcoins through hundreds of transactions. The fact that transactions are so fast and irreversible means that new crimes such as scams and Twitter hacks are now possible.

#4: Easy storage and transfer
As digital assets, cryptocurrencies are easily stored. The storage of the crypto wallet information requires no physical space, as opposed to piles of bills. This means that they do not attract the attention of thieves, nor, most importantly for criminals, of the authorities. Cryptocurrencies are also easy to transfer, both locally and internationally, with no risk of being seized.
Easy transfers set the stage for criminals to both steal and launder funds. Lazarus Group, a cybercrime organization with ties to North Korea, stole $275 million in cryptocurrency from the KuCoin exchange in the largest cryptocurrency theft of 2020. The hack involved a popular money laundering strategy that involves sending stolen funds to mixers in small amounts. Other laundering methods utilized in the hack involved cryptocurrency swaps through decentralized platforms.
Another notorious example appears to be one the largest cryptocurrency heists ever – a theft of $600M from the Blockchain site Poly Network. By exploiting a vulnerability in Poly Network’s system, hackers had taken thousands of digital tokens, such as Ether. The stolen tokens were transferred in small amounts to an online wallet controlled by Poly Networks. The transferred funds eventually amounted to hundreds of millions of dollars.
Both examples also demonstrate the easy, borderless transfers that cryptocurrencies enable.
#5: Borderless
Cryptocurrencies can be transferred quickly and easily from one crypto address to another, whether they serve the same person or totally different parties, locals or foreigners, acquaintances, or strangers. They are easily transferred globally, thus enabling international trading, which, in the criminal setting, translates to trafficking.
Recently, the US Department of Justice announced that a Swedish man responsible for cryptocurrency money laundering and securities fraud had been sentenced to 15 years in prison. This scheme demonstrates both the ease of global transfers enabled by cryptocurrency as well as the lack of trust or familiarity required between parties. This investment scam defrauded thousands of victims in an amount of over $16 million dollars.
The challenge for cryptocurrency investigations
These reasons are also why government security and law enforcement organizations face a daunting task – to detect illicit transactions made by criminals and bring them to justice.
The very benefits of cryptocurrency pose the greatest challenge:
- There is no link between a cryptocurrency address and the person behind it
- Criminals and terrorists can transfer funds globally, easily and quickly
How can Cognyte’s blockchain analytics solution help?
Cognyte’s blockchain analytics solution for cryptocurrency investigations pulls the rug from under criminals and terrorists. It de-anonymizes and reveals illicit transactions made by criminals, thus helping security and law enforcement organizations successfully overcome the challenge of cryptocurrency anonymity.
Based on innovative technology and analytics capabilities, Cognyte enables authorities to reveal cryptocurrency transactions made by known suspects without relying on exchange collaborations, regardless of crypto services such as mixers, shapeshifters, and privacy-enhanced wallets, that are used to obscure the crypto trail.
With Cognyte’s solution, government security and law enforcement organizations can shed light on cryptocurrency crimes in their jurisdiction and gain a valuable new tool to investigate complex cases.
To find out how you can overcome cryptocurrency investigation challenges and tackle this growing threat, we invite you to contact us at: https://www.cognyte.com/contact